
Login / Signup
Cart
Your cart is empty

The thing works like this.
Many coders are unfamiliar with the underlying technologies that make their programs run. But why should you care when your code appears to work? Because you want it to run well and not be riddled with hard-to-find bugs. You don’t want to be in the news because your code had a security problem.
Lots of technical detail is available online but it’s not organized or collected into a convenient place. In The Secret Life of Programs, veteran engineer Jonathan E. Steinhart explores—in depth—the foundational concepts that underlie the machine. Subjects like computer hardware, how software behaves on hardware, as well as how people have solved problems using technology over time.
You’ll learn:
Learn what really happens when your code runs on the machine and you’ll learn to craft better, more efficient code.
Jonathan E. Steinhart has designed graphics hardware and software, and built CAD systems, graphics workstations, circuit simulators, power plants, and languages for integrated circuit design. He has consulted for Apple, Intel, Sun, Welch-Allyn, Lulu, and many others.
Introduction
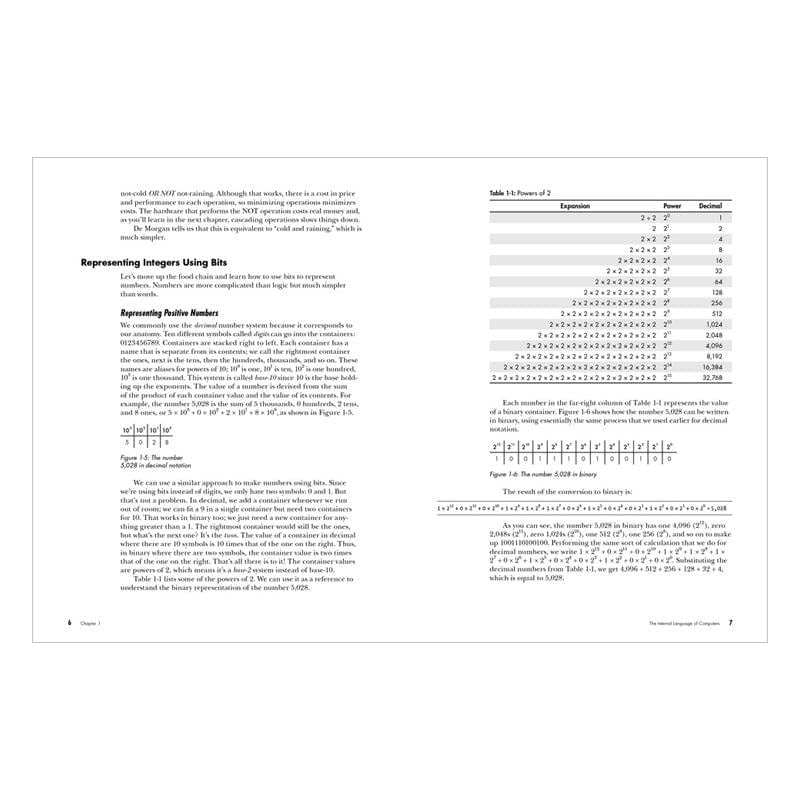
Chapter 1: The Internal Language of Computers
Chapter 2: Combinatorial Logic
Chapter 3: Sequential Logic
Chapter 4: Computer Anatomy
Chapter 5: Computer Architecture
Chapter 6: Communications Breakdown
Chapter 7: Organizing Data
Chapter 8: Language Processing
Chapter 9: The Web Browser
Chapter 10: Application and System Programming
Chapter 11: Shortcuts and Approximations
Chapter 12: Deadlocks and Race Conditions
Chapter 13: Security
Chapter 14: Machine Intelligence
Chapter 15: Real-World Considerations
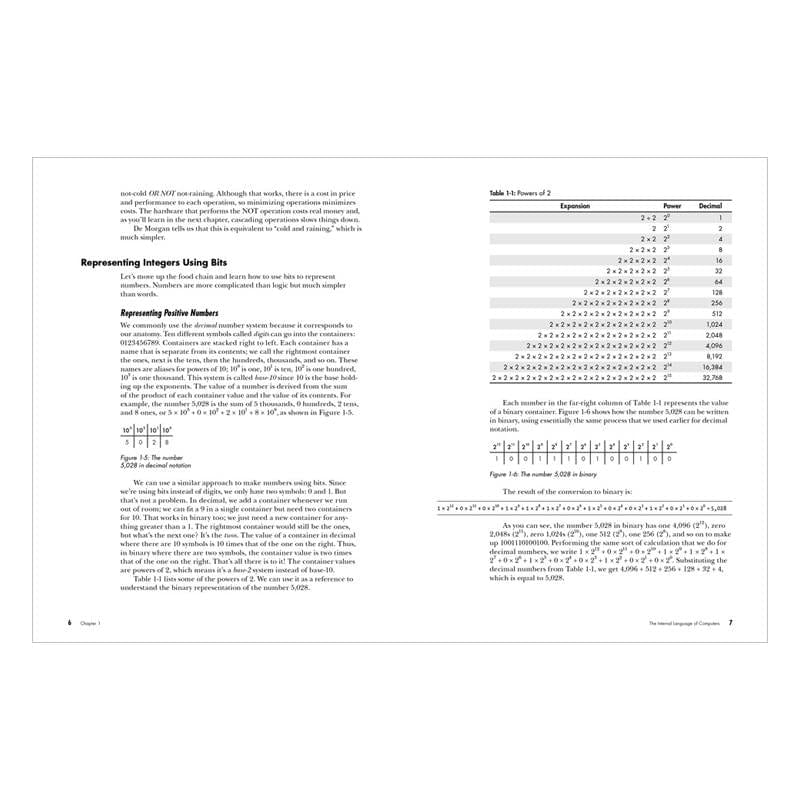
Page 25 The first two lines of Figure 1-16 are incorrect and should read:
0 0 0 0 0 0 0 0 0 1 0 0 0 0 0 1 Unicode A (0x0041)
0 1 0 0 0 0 0 1 UTF-8 A (0x41)